Unlucky Chucky: Uncovering Solonik's personas and origin

For a few months now, a threat actor named Solonik has been actively posting databases on several well-known cybercriminal forums.
We started monitoring this alias on January 12th, when many Instagram users received password reset emails and at the same time an alleged database containing 17 millions Instagram user records was posted on a popular cybercrime forum by the user "Solonik":

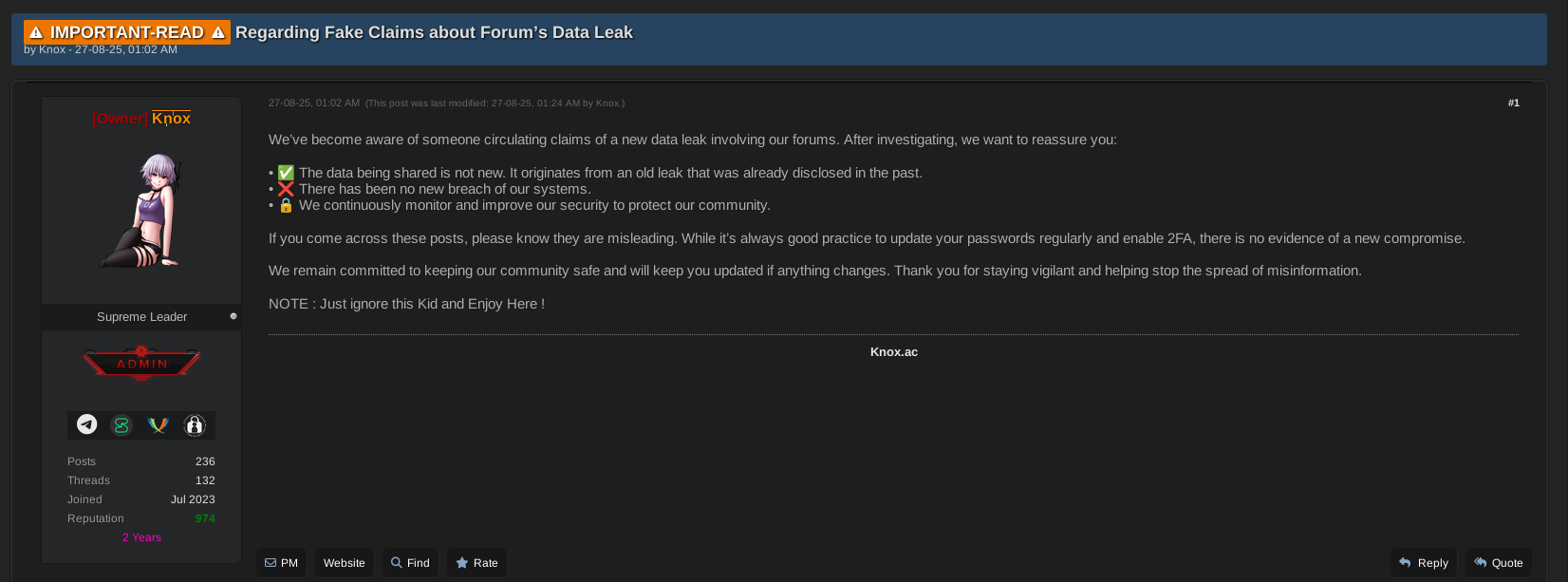
While the alleged database was quickly labelled as an old compilation of Instagram breaches with no freshly dumped data, it brought attention to the Solonik threat actor which kept on actively publishing other databases with alluring names. While doing so, Solonik advertised his Telegram channel, which reached almost 7k followers at its peak.
As we were researching Solonik's activities, we saw in our Twitter feed that StealthMole's experts were quicker than us and published an article explaining their research on the same topic on January, 26th:

The article concludes that the threat actor Solonik has used several nicknames such as Chucky, Chucky_lucky and seems to have ties with iranian and persian-speaking Telegram channels:
Taken together, these findings strengthen the infrastructural linkage between Solonik’s Telegram presence and Iranian-linked Telegram data exposure. The reuse of the same Telegram user ID across multiple usernames, its appearance in leaked Iranian Telegram datasets, and its interaction within regionally aligned Telegram groups suggest operational continuity rather than coincidence. This infrastructure-level overlap does not definitively attribute Solonik to a specific individual or location, but it provides a consistent and traceable framework that aligns with other elements observed throughout the investigation.
We initially planned on writing a long article but considering the heavy work had already been done, we decided to go straight to the point on how we also found Solonik old aliases, and give new insights on Solonik that we found using our investigation platform.
Solonik's personas and activities
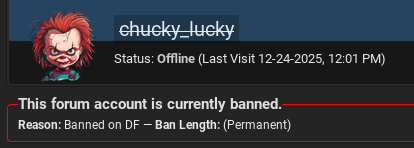
On his Telegram channel, Solonik posted a screenshot of a message he sent to a BreachForums administrator, about an old alias of his he lost access to and wants to reclaim: Chucky_lucky:
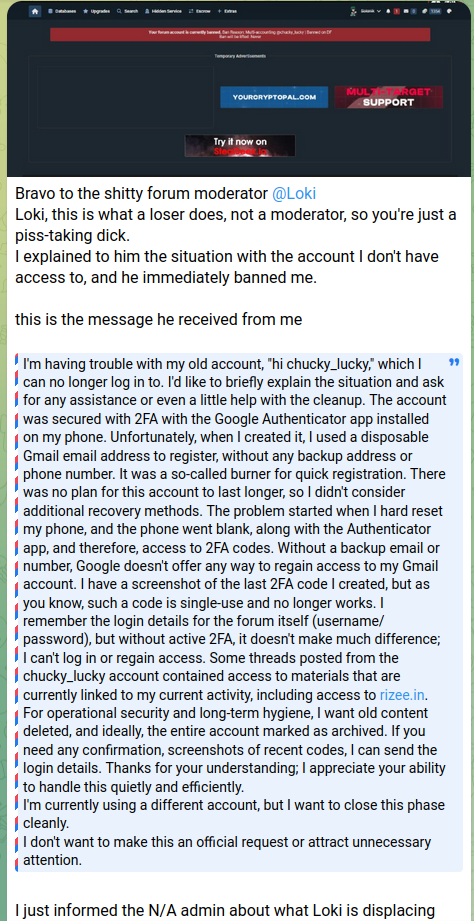
So we have the Solonik=Chucky_lucky link.
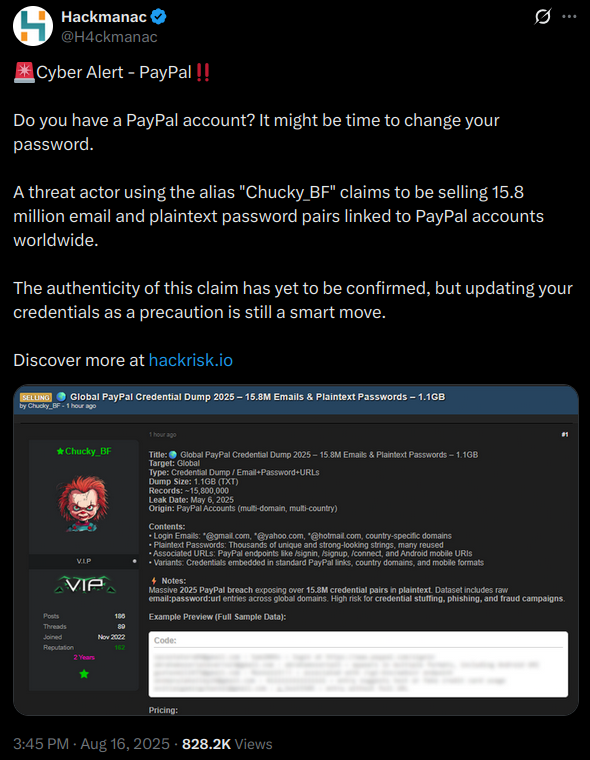
In the screenshot, we can also see that he makes a reference to the hack of "rizee.in" as an "old activity" he now wants to hide. This is interesting: the first thread mentioning this hack was posted on DarkForums on August, 20th, 2025 by someone named Chucky_BF. This alias can also be found on BreachForums. We can therefore assume Chucky_lucky and Chucky_BF are the same person. This is confirmed as in some threads posted by Chucky_lucky on BreachForums archived by our platform, he advertised the Telegram handle t.me/chucky_bf.
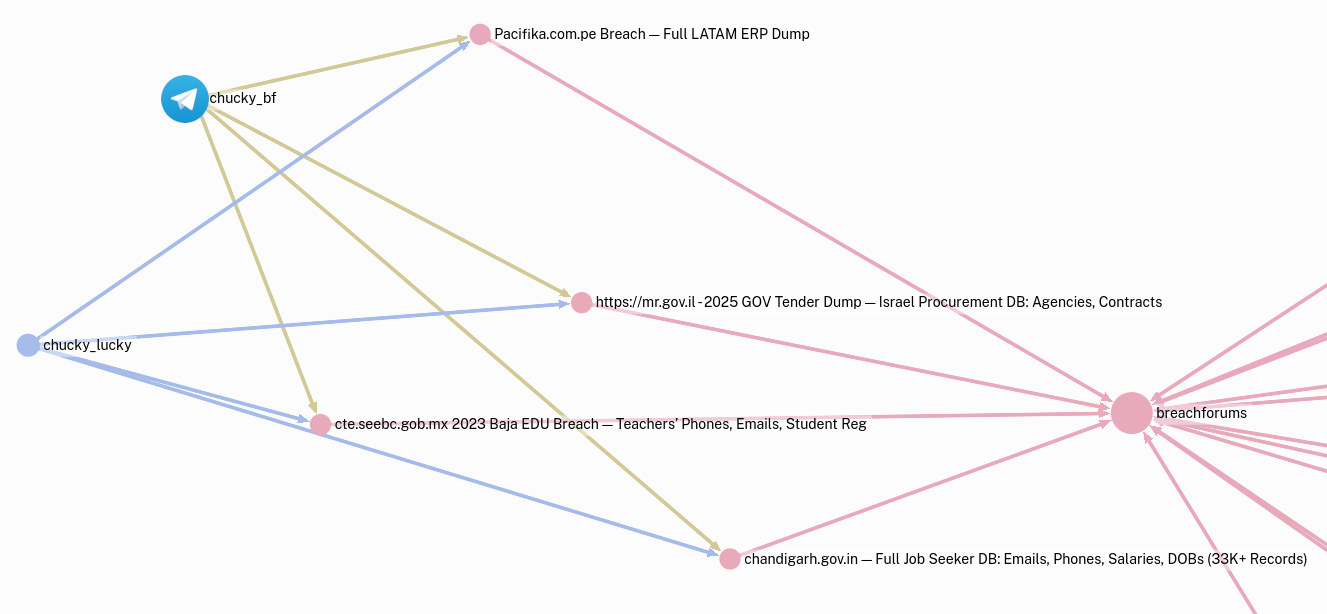
We can now link Solonik to Chucky_lucky and Chucky_BF. The old Chucky_BF alias leads to a lot of activity on cybercriminal forums:
Note that his profile picture shown in the screenshot above is the same as the one he used on his Chucky_lucky handle:
A few more searches later, we found the following thread, mentioning another telegram handle, chucky_leakbasela:
When Chucky got unlucky
Using passive searches, archived data from forums and telegram handles extraction, we were able to retrieve the Chucky* handles used by Solonik. But there is more.
On April 18th, 2025, someone on an Indonesian computer downloaded and executed what appeared to be an infected layededge-bot executable embedding an infostealer. NoxHunt experts were able to retrieve the stolen credentials exfiltrated from this machine. The following accounts information were saved in the victim's browser:
https://breachforums.vc/member.php:chucky_lucky:****
https://breachforums.is/member:chucky_lucky:****
https://breachforums.st/member:chucky_lucky:****...as well as other accounts on hacking websites with the following logins:
Chucky
andinov
andinov666
icebreaker666
cobaylis
cocacolaDid all of these accounts belong to Solonik over time? Not sure: the passwords associated with these last 6 accounts are significantly weaker that the ones used for the chucky_lucky accounts, which could either mean:
- That these are very old nicknames used by Solonik a long time ago ;
- Or that the infected computer is not Solonik's but one he used occasionally, for example belonging to his family, to a friend or to an Internet cafe he went to.
Stolen credentials from stealer data do not come with a date for each entry and only give you the information that URL:login:password entries belong to the same computer. From there, since the infected computer can be shared, one has to be careful to draw any conclusion.
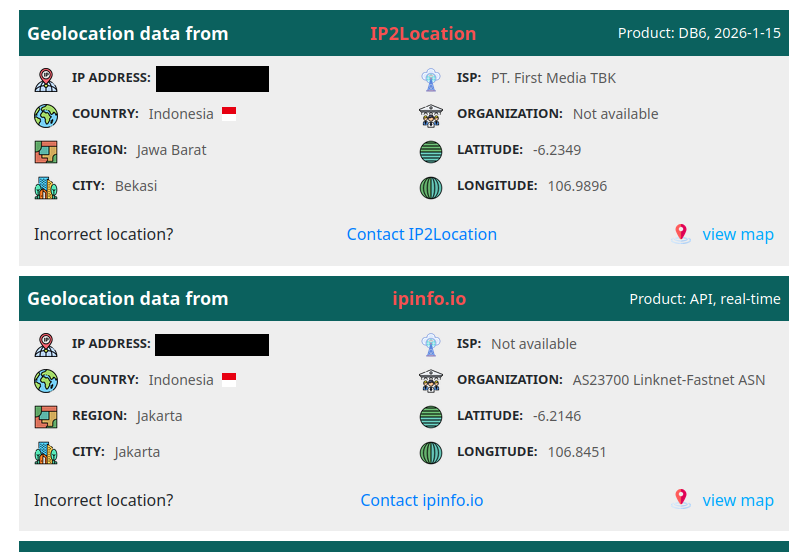
Looking at the stolen credentials and the system information, we noticed entries for several accounts on Indonesian official websites, and that the system language was indonesian. Moreover, the location of the external IP address of the computer network also happens to resolve in Indonesia: we can conclude that Solonik is probably from Indonesia.
To corroborate some of StealthMole's findings, we did find in the stealer data one account on an Iranian cracking website, which could explain why Solonik has indeed shown some presence on the Iranian hacking scene.
Final words
Solonik is an enigmatic actor that was, at some point in time, one of the most prolific poster on Breach and DarkForums. Though, most of that were smoke and mirrors: threads with alluring title but old, recompiled data, attempts at selling publicly available content... After some weeks in the spotlight, almost all Solonik activities have now been wiped: forum threads got deleted, profiles got banned as well as his Telegram channels.
What can be learned from this quick investigation?
- Archiving cybercriminal platforms content is key to keep track of actors ;
- Tracking messaging handles can help you make historical links: threat actors change public aliases often but more rarely their contact handles ;
- Cybercriminals install a lot of cracked software and are not immune to stealers!Stealer data gathering can give you exclusive insights ;
At NoxHunt, we do all that! If you're interested in cybercriminal tracking, subscribe for more!
Et pour les lecteurs français, n'hésitez pas à parcourir nos prestations, et à nous contacter si vous êtes intéressé !
- Solonik associated threads:
DATABASE DATABASE VIETISO.COM — 209K VIETNAMESE TRAVEL CLIENTS + FULL KYC DATA (2026)
DATABASE HORUSDM.COM.BR — MUNICIPAL TAX SYSTEM DATABASES (BRAZIL, 2M+ RECORDS) 14.01.2026
DATABASE [2026] RMONEYINDIA.COM — INDIAN FINTECH BREACH — 1.5GB SQL
COLLECTION PAKISTAN — PTML CELL TOWER GEOLOCATIONS (5M) | KARACHI BTS GRID
COLLECTION EPSTEIN FILES 2024 — FLIGHT LOGS, BLACK BOOK, US COURT DOCS 2026
DATABASE KNOWMYCUSTOMER.IN — 3.4M CORPORATE LEADS — TATA TELE B2B INDIA
DATABASE TEXTITUTE.COM — SMS & CONTACT PLATFORM + CLIENT DB 13.01.2026
DATABASE COSTCO.COM.TW — 526K TAIWAN CUSTOMERS DATABASE (PII + CREDENTIALS)
DATABASE UNSOED.AC.ID — 42K INDONESIAN UNIVERSITY STUDENT RECORDS + EMAIL, PHONE, ID
DATABASE UNSOED.AC.ID — 42K INDONESIAN UNIVERSITY STUDENT RECORDS + EMAIL, PHONE @Solonik_BF
DATABASE KAZAKHSTAN — NATIONAL CITIZENS DATABASE (INN, DOB, FULL NAMES) @Solonik_BF
DATABASE US MILITARY AIRPORTS — FULL COORDINATES & FAA DATA (STRATEGIC SITES) @Solonik_BF
DATABASE SYSTAGG.COM.BR — 100K FULL BRAZILIAN CANDIDATE PROFILES + CPF + EMPLOY @Solonik_BF
DATABASE IHEC.IQ — 4.5M IRAQI VOTER RECORDS (FULL ELECTORAL DATA) @Solonik_BF
DATABASE 321K SEEDS PHARSE ETHERNUM 2026 @Solonik_BF
DATABASE FGTS.GOV.BR — 1.5M BRAZILIAN PENSION RECORDS (FULL CPF + SALARY HISTORY) @Solonik_BF
DATABASE EPU.EDU.IQ — ERBIL POLYTECHNIC STUDENT & TEACHER RECORDS + FILES @Solonik_BF
DATABASE IRGC.GOV.IR — 240K IRANIAN REVOLUTIONARY GUARDS (FULL IDENTITY + CONTACT) @Solonik_BF
DATABASE WA.IRAN — 1.2M WHATSAPP USERS (MOBILE NUMBERS ONLY, 2024) @Solonik_BF
DATABASE MODHOSPITAL.KR — 45K KOREAN HOSPITAL PATIENT & SYSTEM RECORDS 14.01.2026 @Solonik_BF
DATABASE FUSE.CO.ID — 199K INSURANCE RECORDS + FULL POLICY + KTP/EMAIL/PHONE 2026 @Solonik_BF
DATABASE TEXTITUTE.COM — SMS & CONTACT PLATFORM + CLIENT DB 13.01.2026 @Solonik_BF
DATABASE IRANCELL — NATIONAL TELCO DUMP | 60M CUSTOMERS | .MDB FORMAT @Solonik_BF
DATABASE IWINV.KR — 144K KOREAN VPS HOSTING USERS + LOGIN (FULL SQL DUMP) @Solonik_BF
DATABASE ACUITY.COM — 9M ILLINOIS INSURANCE CUSTOMERS (FULL US HEALTH/DEMOE) @Solonik_BF
DATABASE FCBB.COM — USA BROKERAGE DATABASE + NDA + LOI + LISTING DOCS (FULL) @Solonik_BF
DATABASE SNT-RF.RU — 9.9K RUSSIAN NON-COMMERCIAL GARDENING ENTITIES (FULL CORP DUMP)
DATABASE BODOGLIFE.COM — 24.9K US GAMBLING USERS (FULL DATABASE, 2026)
DATABASE JAPAN/CHINA WEB CORE — FLIPPA.JP / GUITARME.CN / KSOURCE / MHR / PREPASS @Solonik_BF
DATABASE [2026] RMONEYINDIA.COM — INDIAN FINTECH BREACH — 1.5GB SQL | @Solonik_BF
DATABASE LPSE.DEPHUB.GO.ID — 735K+ INDONESIAN GOVT TENDERS & WINNING CONTRACTORS | @Solonik_BF
DATABASE VIETISO.COM — 209K VIETNAMESE TRAVEL CLIENTS + FULL KYC DATA (2026) @Solonik_BF
DATABASE RIZEE.IN — 100K STUDENTS + 14.8M QUESTIONS | Breached 10.01.2026
DATABASE OSSESANJUAN.COM.AR — 98K GOV (ARGENTINA, 2026 DUMP)
DATABASE BTCONNECT.COM — 49.9K UK CRYPTO CLIENT RECORDS (2025 DATABASE LEAK) @Solonik_BF
DATABASE portalicmsdipam.saovicente.sp.gov.br — FULL DIPAM DATABASE - 8 JAN 2026 | @Solonik_BF
DATABASE CHAINLINK.ORG — 6K WEB3 INVESTORS W/ EMAIL + ETH WALLETS + AMOUNTS @Solonik_BF
DATABASE DUBAI CRYPTO — 104 UAE HNW INVESTORS (FULL EMAIL LIST, 2025) @Solonik_BF
DATABASE LUMINPDF.COM — 15.4M USERS EXPOSED (EMAIL, HASHES, TOKENS, GENDER, LANG) —@Solonik_BF
DATABASE HORUSDM.COM.BR — MUNICIPAL TAX SYSTEM DATABASES (BRAZIL, 2M+ RECORDS) 14.01.2026
DATABASE IRAN TELCO DATASET — FULL PII DUMP (ICCID, ID, ADDR, GSM) @Solonik_BF
DATABASE KPS.KU.AC.TH — THAI UNIVERSITY SERVER SQL DUMP (AGRICULTURE + ECOM) 8 JAN 2026
[SALE] mail.gdt.gov.vn OWA Access – Vietnam Tax Authority Employee Mailbox
DATABASE CHINA CITIZEN DATABASE — 1.2B RECORDS WITH NAMES, IDS, GPS, MOBILE | @Solonik_BF
RIZEE.IN — 100K STUDENTS + 14.8M QUESTIONS | Breached 1- Chucky_lucky latest threads:
cte.seebc.gob.mx 2023 Baja EDU Breach — Teachers’ Phones, Emails, Student Reg
Pacifika.com.pe Breach — Full LATAM ERP Dump
https://mr.gov.il - 2025 GOV Tender Dump — Israel Procurement DB: Agencies, Contracts
chandigarh.gov.in — Full Job Seeker DB: Emails, Phones, Salari

