Inside the computers of DPRK 🇰🇵 IT workers

Key points
- On April 8, @ZachXBT published an investigation into DPRK 🇰🇵 overseas IT workers and their payment infrastructure.
- The breach originated from a compromised DPRK worker device infected by an infostealer, exposing internal communications via luckyguys[.]site.
- The operation reflects a large-scale but relatively low-sophistication ecosystem of fraudulent remote IT work.
- Using STEALINT, researchers pivoted from ZachXBT’s findings to attribute activity and reconstruct operator profiles.
- Infostealers are not just threats — they are powerful cyberdefence tools for investigations.
- This case demonstrates how infostealer telemetry can turn adversary compromise into actionable intelligence.
- Key Analytical Takeaways:
- DPRK IT worker operations rely on:
- VPN obfuscation with Astriil VPN
- Fake identities and portfolios
- Freelance and remote job platforms
- Extended use of AI copilot tools during their job interview
- They seem to be focused on the Middle-east region (Dubai and Saudi Arabia)
- Operators demonstrate moderate technical skills but strong operational scaling.
- Activities span beyond work: Crypto, gambling, and side-platform usage suggest diversified revenue or personal use.
- DPRK IT worker operations rely on:
On Apr. 8, @ZachXBT published an investigation on North Korean abroad IT workers and how they manage payments with their home country. According to the thread, the breach originated from a compromised DPRK IT worker device infected by an infostealer, which provided access to internal communications via a platform called luckyguys[.]site. This system functioned as a payment reporting hub, allowing overseas workers to relay earnings back to their handlers.
The findings suggest a large-scale but relatively unsophisticated ecosystem of fraudulent remote IT work, generating significant revenue for North Korean networks. While less advanced than known operations like AppleJeus or TraderTraitor, this cluster highlights the breadth of DPRK cyber-enabled financial activity.
You can find the full thread here:
1/ Recently an unnamed source shared data exfiltrated from an internal North Korean payment server containing 390 accounts, chat logs, crypto transactions.
— ZachXBT (@zachxbt) April 8, 2026
I spent long hours going through all of it, none of which has ever been publicly released.
It revealed an intricate… pic.twitter.com/aTybOrwMHq
...And read the full article here:

Full article by Zach. Password is 123456.
Using the technical elements from Zach's findings, we were able to retrieve infostealer data associated with two DPRK workers from our STEALINT platform.
Here is their story.
Hero#1: Meet SuperDev
SuperDev was infected by an infostealer on March, 15th 2026. He uses a Windows 11 OS installed on december, 2025 with Korean English language. His external IP was geolocated in the US, and associated with AstriilVPN, as mentionned by Zach.
Profiling the computer specs
From the list of the processes running on SuperDev's computer, we can assume he is running some kind of full-stack webdev work (code.exe, sublime_text.exe, node.exe, multiple postgres.exe). On the networking side, he has running instances of AstriilVPN, which is consistent with the external IP observed, and DeskIn, a remote desktop tool (https://deskin.io/) he probably used for remote work. SuperDev also uses Telegram, Slack, LibreOffice and Lightshot.
The list of installed software on SuperDev's machine confirms what we saw from the running processes: tools like VisualStudio, Git, Postman and Android Studio probably used for webdev. However, this list also reveals a data science and AI stack: Python, Anaconda, and use of an Exodus crypto wallet, QQPlayer and IP Message.
Diversity of tools used by SuperDev shows that he is probably a flexible freelance doing various development jobs. IP Messenger (Japanese), QQPlayer (China) and AstriilVPN are mostly used in Asian countries.
As of yet, we cannot conclude SuperDev is indeed from North Korea, as elements from his computer specs seem to only point to a regular korean-speaking engineer searching for freelance dev work. But looking at his web accounts is where it gets truly interesting.
Looking at SuperDev's web accounts
Continuing to dig into stealer data associated with SuperDev, we analyzed the 263 websites he saved credentials for.
Two major patterns stand out from these websites : multiple URLs and logins that show that SuperDev have been developping multiple websites for clients, and several websites related to jobseeking platforms but also fake personas and AI-based helpers for job interviews.
GITHUB account
SuperDev owns the Github profile Perfectwork829 which was still active as of April, 2026. This profile, active since March 2023, is 30 repos deep but shows several hallmarks of a fake or freelance-for-hire account.
The most glaring red flag is the presence of three separate portfolio sites with different names — amalPortfolio, oleksiiPorfolio, and myportfolio — strongly suggesting the account is used to build fake GitHub credibility for multiple different people. The sports betting theme appears no fewer than four times (sportsBetting, sports-betting-newversion, sports_betting_stepper, and a forked ML repo), which reads less like genuine interest and more like recycled work sold repeatedly. The repos worth noting technically are react-reduced-project (the only one showing awareness of modern tooling with Qwik and DaisyUI) and the Laravel suite, which at least demonstrates some backend breadth. The brand-new fullstack_dev_portfolio in Vue, created April 2026, fits the pattern of assembling yet another identity. Overall, a profile built to look experienced rather than to document real development work.
Web development work
A major pattern is the abundance of local and staging URLs (localhost, 127.0.0.1, private IPs), indicating ongoing development, testing environments, and possibly multiple projects running in parallel. The inclusion of Figma previews and job/freelance platforms further supports the idea of a product-building or freelance workflow, combining development, design, and client acquisition.
For payments, SuperDev seem to mostly rely on Paypal and Stripe.
Jobseeking platforms and copilots
SuperDev has accounts on the following platforms:
- https://www.xing.com
- https://fldata.snaphunt.com
- https://app.jobscan.com
- https://myworkdayjobs.com
- https://empleo.coremain.com
- https://jobs.x-team.com
- https://www.cybercoders.com
- https://www.totaljobs.com
He also used several ai-powered copilot tools to boost his interviews:
- https://jobright.ai/
- https://www.ntro.io/
Other interesting findings
SuperDev also used some virutal phone SMS provider such as SMSPool.
There are also scattered domains related to gambling, gaming and financial platforms (crypto, trading, FOREX):
- Gambling:
- bcgame.li
- bcvn2.com
- slotstemple.com
- Gaming:
- Roblox
- Seafight
- Xbox
- Trading / Crypto / FOREX:
- https://www.xmtrading.com/
- https://www.xmglobal.com/
- https://www.mexc.com/
- https://www.okx.com/
- https://www.bitrue.com/
- https://www.mql5.com/
SuperDev multiple identities
Using stealer data, we can confirm that the following allegations are correct and linked to our SuperDev guy:
New DPRK front found!
— Fox_threatintel (@banthisguy9349) April 9, 2026
Fake Front company verityai[.]co
Fake accounts https://t.co/8MO3HQGcothttps://t.co/652sHKcDPChttps://t.co/kH1YbdArXw https://t.co/JxuQVEG4jM
75% chance of being fake as well.https://t.co/y7BZxn3q0R
We can also add that SuperDev has worked on the following websites according to stealer data:
- http://www.box12ksa.com/
- https://3daysksa.com/
The first website is related to a likely fake gym, and the second one seems to impersonate a real gym brand, both in Saudi Arabia. The fake X accounts associated with these websites are boosted by fake followers. Continuing our research we found that both websites were advertising APK associated with a company named Memvera on APKPure:
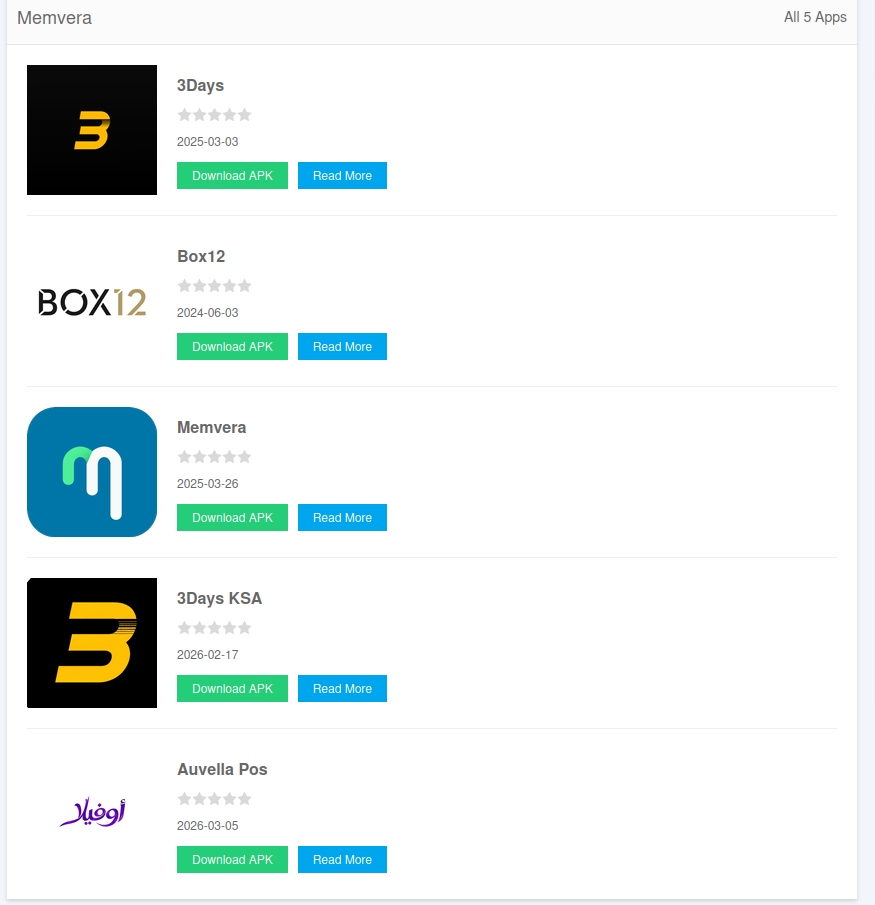
Memvera happens to be linked to the Shijazi88 persona mentioned in Fox_threatintel's post: on the website https://shijazi.me, a person named Safwan Hijazi claimed to be "CTO & Co-Founder @ ProMatrix / memvera". He seems to own the X account https://x.com/shijazi88, which has the same handle as the Github account https://github.com/shijazi88.
This leads to 3 possibilities:
- Shijazi is a fake persona created by DPRK worker SuperDev to make money (highly-likely)
- Shijazi and the Memvera company are impersonated by SuperDev (likely)
- Shijazi and Memvera hired SuperDev to develop their websites and APK (unlikely)
Hero#2: Meet DevWisdom
DevWisdom was infected with Vidar stealer in late december, 2025. His setup is pretty similar to SuperDev's, with an external IP address located in Japan and associated with Astriil VPN ranges.
Computer specs
DevWisdom's running process and installed software indicate a technically experienced user who primarily works with development tools and local environments. The presence of Node.js, Python, and Git suggests regular involvement in programming, likely including backend development, scripting, or automation. The use of both PostgreSQL and MongoDB indicates familiarity with different database systems and data models. The system also includes VMware Workstation, which points to the use of virtual machines for testing backend solutions.
Networking and remote access tools are also present. The user has Astriil VPN running, just like our SuperDev guy, showing that DPRK workers seem to consistently use this VPN, very popular in Asia. Additionally, AnyDesk indicates the user may access or manage systems remotely.
Overall, the environment is consistent with someone interested in web development, front and backend, which happens to be very similar to SuperDev's.
DevWisdom's web accounts
Using stealer data, we found the personal fake portfolio of our suspect, where he claims to be a full-stack developer from Malaysia. On the website, we found a link with his GitHub handle: DevWisdom08.
GITHUB account
DevWisdom08 is a recently created GitHub account (November 2025–February 2026) with 13 repositories spanning six languages, which is unusually broad for such a short timeframe and raises questions about authenticity.
The most structurally interesting work is the ISP SaaS suite — three separate repos (isp-saas-platform in Go, isp-saas-frontend in Vue, and isp-agent in Go) that together suggest a full-stack product, with isp-agent being the only repo to have earned a star. Football-Arena (Dart/Flutter) and rapresentante-commercianti (a Flutter loyalty system MVP for local Italian merchants) stand out as the most concrete, domain-specific projects with actual descriptions. The AI-character-platform (TypeScript) and movesbook-nextjs are the most recent additions and follow current market trends closely. Overall, the profile reads less like an organic developer journey and more like a portfolio assembled quickly to appear credible — the lack of READMEs, descriptions, and community engagement across most repos reinforces that impression.
Main pattern: job searching (tech-focused)
A large portion of DevWisdom's account history is clearly related to job platforms and applications:
- Shopify signup
- Workday-based career pages (multiple companies)
- Randstad applications
- Wellfound
- Remote.co
- Hubstaff Talent
This suggests that our hero#2 was actively searching for jobs, focusing on remote or international roles as a front and back-end developer, as well as cloud admin and web3 dev.
Portfolio / project activity
We also noticed several accounts related to portfolio and CV platforms with several different names:
- Netlify / Vercel links
- Figma site
- portfolio-style domains
This indicates that DevWisdom was trying to improve his visibility by creating fake experienced-developer personas to better apply for jobs and build credibility.
-- That will be it for their story. On to the next one...
Want to monitor infostealer infections and mitigate intrusion risks for your company?

